
Many people use short passwords, simple words, or include numbers in the passwords that can relate to their lives and are still too easy to guess. Sometimes if a person has difficulty remembering passwords, they get a list of the passwords right next to the computer. So yes, people do it even after knowing this can compromise their safety if others use their computer or get their hands on the list.
However, too strong passwords that a person can't remember are useless. Also, passwords that are too easy to remember can be easy to guess or establish with a brute-force attack. Hence setting up a strong password is more cakewalk than it seems. You must consider too many aspects before choosing a unique password each time, wondering what? Scroll down and look at the below section to learn how to easily create a strong password.
What Makes a Password Strong?
The critical aspects of a strong password are:
- Length- as the longer the password is, the better it is for the user,
- A mix of letters- both the upper as well as lower case,
- The numbers- ensure it’s not easy to guess the number,
- Various symbols- no ties to the personal information of the user and no dictionary words.
The good news is that you don’t have to memorize many awful strings of random letters, numbers, and symbols to incorporate all of these aspects into your passwords. Instead, you need to learn a few tricks.
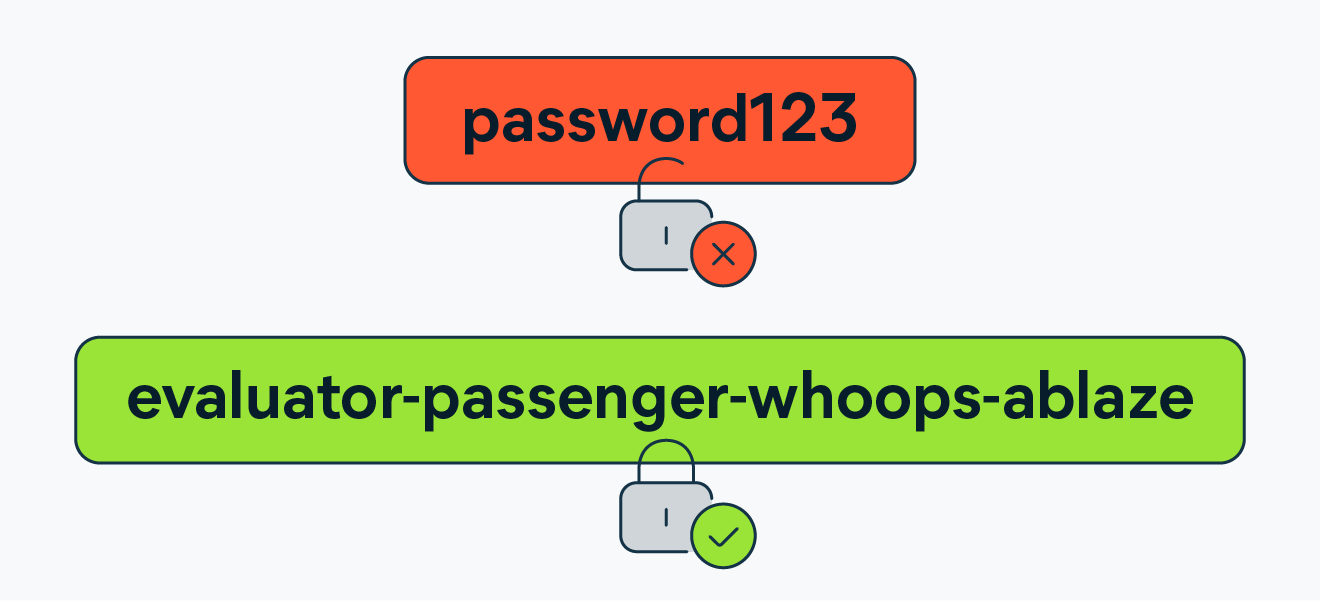
According to a study, a good password has a minimum of 12 characters. It would be best if you chose a password that is long enough. Everyone agrees on no minimum password length, but you should always go for passwords with a minimum number of 12 to 14 characters in length.
The longer the password, the better it will be. This may include numbers, symbols, Capital Letters, and lowercase letters. You can use a mix of different types of characters to make the password much harder to crack.
It should not be a dictionary word or a combination of dictionary words. You must always avoid the famous dictionary and varieties of dictionary words. Any dictionary word on its own is a terrible password. Combining a few words is also a terrible password if they are ubiquitous.
You should not ever reuse your passwords. Suppose you are using the same password across your email, shopping, and other social media handles and websites that are holding sensitive personal data. In that case, if one of them is hacked, you will be exposed to all other services at the risk of being breached as well.
You should not also share your passwords. This one is a no-brainer; even if you need to share it, you'll need to change it as soon as possible.
Use Emoticons
You can always use emoticons if you want to add symbols to your passwords without making them harder to remember.
Although you won't be able to add emojis to a password, you can use emoticons, the coded versions of emojis usually made up of punctuation, letters, and numbers. They are also a great way to create unique passwords.
Use a Password Generator
If you don’t have time or patience to develop strong passwords, a password generator is a quick and easy way to get a unique and strong password. A password generator will generally create a sequence of random characters.
You can copy the password from it and use it as a password for their devices, email, social media account, or anything else requiring private access. This is a great way to create strong passwords, but they must remember them.
How does a Password Get Hacked?
Cybercriminals generally have several password-hacking tactics for their use. The easiest one is to access the passwords from the dark web. There are large sums of money in the buying and selling of login credentials and passwords on the black market, and if you have been using the same password for many years, there are chances that it has been compromised.
If a person is wise enough to keep their passwords off the aggregated Blackmarket lists, cybercriminals will have to crack them. There are many ways in which they can accomplish it. They are:
Brute Force Attacks
This time of attack generally tries to guess every combination in the book until it hits the right password. The attacker generally uses software to try as many combinations as possible and quickly as possible. Unfortunately, there have been some unfortunate headway in the evolution of that kind of technology.
In 2012, an industrious hacker unveiled a 25-GPU cluster he had programmed that can be used to crack any 8-character Windows password, which has both uppercase and lowercase letters, numbers, and symbols in less than six hours.
It can try more than 350 billion guesses per second. Generally, any password with under 12 characters is vulnerable to being cracked and the account being hacked. From this, we can see how a long password is better.
Dictionary Attacks
This attack is what it sounds like. The hacker attacks you by using a dictionary. A brute force attack generally tries every combination of symbols, numbers, and letters. Still, a dictionary attack generally tries a prearranged list of words, such as the ones you can find in a dictionary.
If your password is a common word, it will only survive a dictionary attack if the word is wildly uncommon or you’ve used multiple-word phrases.
Phishing
This is the most terrible type of cyber attack. It happens when cybercriminals try to trick, intimidate, or pressure a person through social engineering into unwittingly doing what they want.
A phishing email may tell a person that there's something wrong with their credit card or bank account. They will also direct the person to click a link, taking them to a phoney website that resembles the bank or the credit card company.
Phishing scams can also try to trap a person through phone calls too. Yes, you can get any robocall claiming to be from their bank or credit card account. However, you should always notice the recorded greeting because they generally don't specify which credit card it's calling about.
It's generally a test to see if a person hangs up right away or if they've got a person hooked to share his/her details with them. If a person stays on the line, they will soon be connected to a natural person who will do what they can to take as much sensitive data out of the person as possible, including their passwords, to rob them or harm them in any way possible according to their needs.
How to Create Strong Passwords
Creating a strong password always seems challenging, especially when the job is to create a unique password for each of the sites you visit. As a result, many people use one identical password even though they know it's unsafe, and if it gets compromised, all of their web information will be exposed.
If you find yourself in a similar kind of state, follow the below processes to create strong passwords next time onwards and change the existing ones.
The Revised Passphrase Method
This is the multiple-word phrase method for creating a strong password with a twist. You can choose bizarre and uncommon words to create a strong password by this method. Use proper nouns, local businesses or shops, historical monuments, words you know in another language, etc.
A hacker might guess the word, but he or she would need help to guess a good password with a combination of many words. While the words should be uncommon, they should also try to compose a phrase with a mental image to help them remember it.
To add another notch in the password complexity, one can add random characters in the middle of the words or between the words they have used. In this method, you have to avoid the underscores between words.
The Sentence Method
This method is also popularly known as the "Bruce Schneier Method." The idea is to think of random sentences and then transform them into passwords using a rule to remember them.
Ways to Improve the Password
All of the above methods written here generally help strengthen passwords and are widely used. Still, they could be more workable because an average person uses dozens of them. Here are a few ways to use modern technology to make strong passwords.
Use a Password Manager or Random Password Generator
A password manager generally keeps track of a person's passwords and does all the remembering for him/her, except for the master password, which grants them access to their password manager.
Careful about Password Sharing
Security-conscious websites generally hash their users' passwords to remain encrypted even if their data gets out to the public.
Other websites generally only bother with this step. Before starting any account, creating passwords, and giving a website very sensitive info, an individual should always consider assessing the site.
They should always look for factors like does it have https in the address bar, which will ensure a secure connection. Do they get the sense it is up to the newest security standards that are available today? If these questions still need to be fulfilled, you should think twice before creating an account.
Use Multi-factor Authentication.
Multi-factor authentication (MFA) generally adds extra protection to any of your data. It generally becomes the first layer of protection if a person's account details ever get leaked.
These have become the new industry standard for adequate security. They generally require some extra security other than passwords like biometrics such as fingerprint or iris scanners.
Use an Authenticator Smartphone App
The best MFA method for a person is using a specialized smartphone app. This kind of app generally generates a one-time PIN that a person can enter as an additional factor during their login process. The PINs automatically change every 30 seconds. They must follow the instructions to set up MFA for any application needing protection.
The Security keys
Security keys generally take security to the next level. A security key like the YubiKey gives a person the most state-of-the-art protection that is available nowadays. It generally serves as an MFA, granting individuals access to their files only if they physically have the key.
Security keys are usually available in the USB, NFC, or Bluetooth versions and are generally about the size of a thumb drive.
Additional Security Tips that are Surrounding Passwords
You can protect your login information further with this type of common sense, high-security tips such as
- Use a VPN when on public Wi-Fi. That way, when you log in to any of your accounts, no one intercepts your username and password.
- You should never text or email anyone your password.
- When selecting any security questions for yourself while creating an account, you should always choose quite hard questions to which only you know the answer.
Note: This could be any personal data that nobody knows. Many of the questions that a website generally asks have easy-to-find answers in the various social media channels with a simple search, so you should be aware of that and choose the questions carefully.
- When you are done, you should always take the time to tell your family and friends to protect themselves too.
- You should always make sure that his/her antivirus is up-to-date. If a threat somehow gets past their strong defences and into their system, a good antivirus will always detect and neutralize it.
Things you Should Not Include in a Password
When updating and creating new passwords, you should not include the following information in your passwords-
- Your pet's name.
- Your birthday or that of any of the family members.
- Any words that are related to your hobby, job, as well as interests.
- The part of your home address, including the city/town, the street, the house/apartment number, or the country you live in.
- Your name or the name of a family member or the family title.
Cybercriminals generally first research their victims online, looking for clues to help them hack the password. And they always create passwords from these types of clues about the person.
Suppose any of the passwords use any information linked to a person; in that case, you should always take a few minutes to update your passwords following the strong password practices discussed here.
Conclusion
The passwords generally grant access to all the personal kingdoms. So you must always think of the best practices to create a strong password to protect your accounts against cybercriminals. If the passwords you use were part of a breach, change them immediately.
As mentioned, you should always choose a strong password, but you may also need to do more than that sometimes. Using stronger passwords will only sometimes keep you secure from all the kinds of threats out there, but using a VPN connection will do. Reputed providers like VPN Surf mask your IP address and hide your location to protect your passwords from prying eyes.
Do you value your privacy online?
Use VPN Surf and surf safely and securely in the open waters of the internet.
