Encryption is a fantastic development in modern-day computing. It keeps your data safe and sometimes even allows for private communication between 2 or more machines, like in the case of using a VPN. In the past couple of years, it has become a staple in the internet culture, with most users refusing to visit sites without an encryption method such as a TLS or SSL and switching to encrypted instant messaging apps.
Unfortunately, to every good side of technology, there also has to be a negative one. Encryption can be and has been weaponized by malicious software developers in order to extort money from individuals, businesses and even governmental organizations. This type of malware is called ransomware and it works by encrypting all the data on the target machine and demanding a ransom to be paid in order to provide a key so that the data can become accessible again.
What is Snatch Ransomware?
Snatch is a newly discovered ransomware variant that bypassed Window’s endpoint protection by rebooting the device in Safe Mode. It works because some antivirus software does not start in Safe Mode, and the developers discovered that they could easily modify a Windows registry key to boot your PC into Safe Mode.
The Snatch ransomware is a crypto-virus that first surfaced at the end of 2018 and targeted prominent targets like the hosting company SmarterASP.net. But a brand-new, distinctive strain of Snatch has emerged in the wild. Hackers are continually developing ransomware distribution methods; however, there aren't many of them.
How does snatch ransomware work?
The trick here entails rebooting customers' computers into Safe Mode and encrypting stuff. Because some antivirus programs won't launch in Safe Mode, this technique works. The creators of the Snatch ransomware identified a way to boot into Safe Mode by using a Windows registry key, which allowed them to launch the malware undetected by antivirus software.
Once the target machine is booted into safe mode, the ransomware encrypts your files. To encrypt these files, the hackers attempt to extort money from you by soliciting ransoms in the form of Bitcoin (i.e. making it untraceable back to them). The Readme Restore Files.txt text file that the Snatch ransomware downloads after encrypting the files contains a ransom demand stating that between 1 and 5 Bitcoin must be paid in exchange for the decryption key.
For comparison, the current value of 1 Bitcoin is approximately £5,573. In March 2019, the Snatch ransomware switched from targeting regular users with spam emails to corporations, occasionally labeling their ransom notes with the company's name.
Which files are targeted?
Snatch targets specific files with extensions .doc, .docx, .xls, .pdf and many more. It changes these extensions to Snatch, so they are unopenable. Once the executable file is run, it creates a Readme_Restore_Files.txt note in which the hacker demands anywhere between 1 and 5 Bitcoins in exchange for the decryption key. It looks like this:
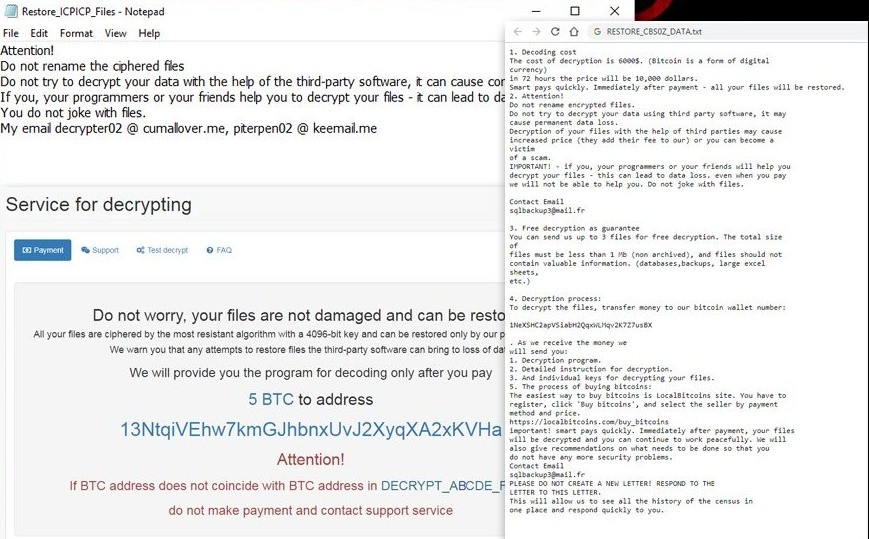
Since the software uses AES encryption, infected files are not decryptable without a key. Snatch ransomware files, currently, are not decryptable, as the malware developers use sophisticated AES encryption. If your machine has become infected with the Snatch ransomware and your files are encrypted, restoring your files from a recent backup is the best course of action. Paying the ransom not only encourages this increasingly lucrative strand of cyber criminality, but there’s no guarantee you’ll even get your data back.
If you don’t have an up-to-date backup, there isn’t much you can do other than sit on your data until security experts create a decrypter for the Snatch ransomware – which could take years. To protect yourself from ransomware attacks, avoid opening email attachments from untrusted sources, especially emails sent to your Junk folder. Always download software from trusted sources.
How can you guard against ransomware infections?
Never click on links or attachments included in emails you get from unknown, shady, or questionable email accounts. Most of the time, these emails are portrayed as important and official; do not click any website links or open any attachments. Download software from reputable, authoritative sources and direct links.
Use only trusted sources; avoid using third-party downloaders, installers, or peer-to-peer networks. These sources frequently advertise malicious software capable of infecting computers or causing other severe issues. Operating systems and installed applications should be upgraded using tools or functional implementations provided by authorized software developers.
What is the most common method of snatch ransomware?
The most common methods to spread ransomware-like software and other computer viruses are spam campaigns (emails), dubious software download sites, Trojans, software cracking tools, and bogus updates. Cybercriminals spread these infections by passing off genuine infected email attachments (or links).
Is it okay to use software-cracking tools?
Because they are illegal (using them is a cybercrime) and frequently result in computer viruses, software cracking tools should not be trusted. Install and keep active an anti-virus or anti-spyware program you can trust on your computer to keep it safe.
Typically, these tools identify and eliminate dangers before they cause any harm. We advise conducting a scan with Combo Cleaner Antivirus for Windows to detect and remove Snatch if it has already infected your machine.
Conclusion
Because of malicious software like Snatch and thousands more, we always recommend for you to create backups of important files and be extra vigilant when downloading things from the internet.
Do you value your privacy online?
Use VPN Surf and surf safely and securely in the open waters of the internet.
