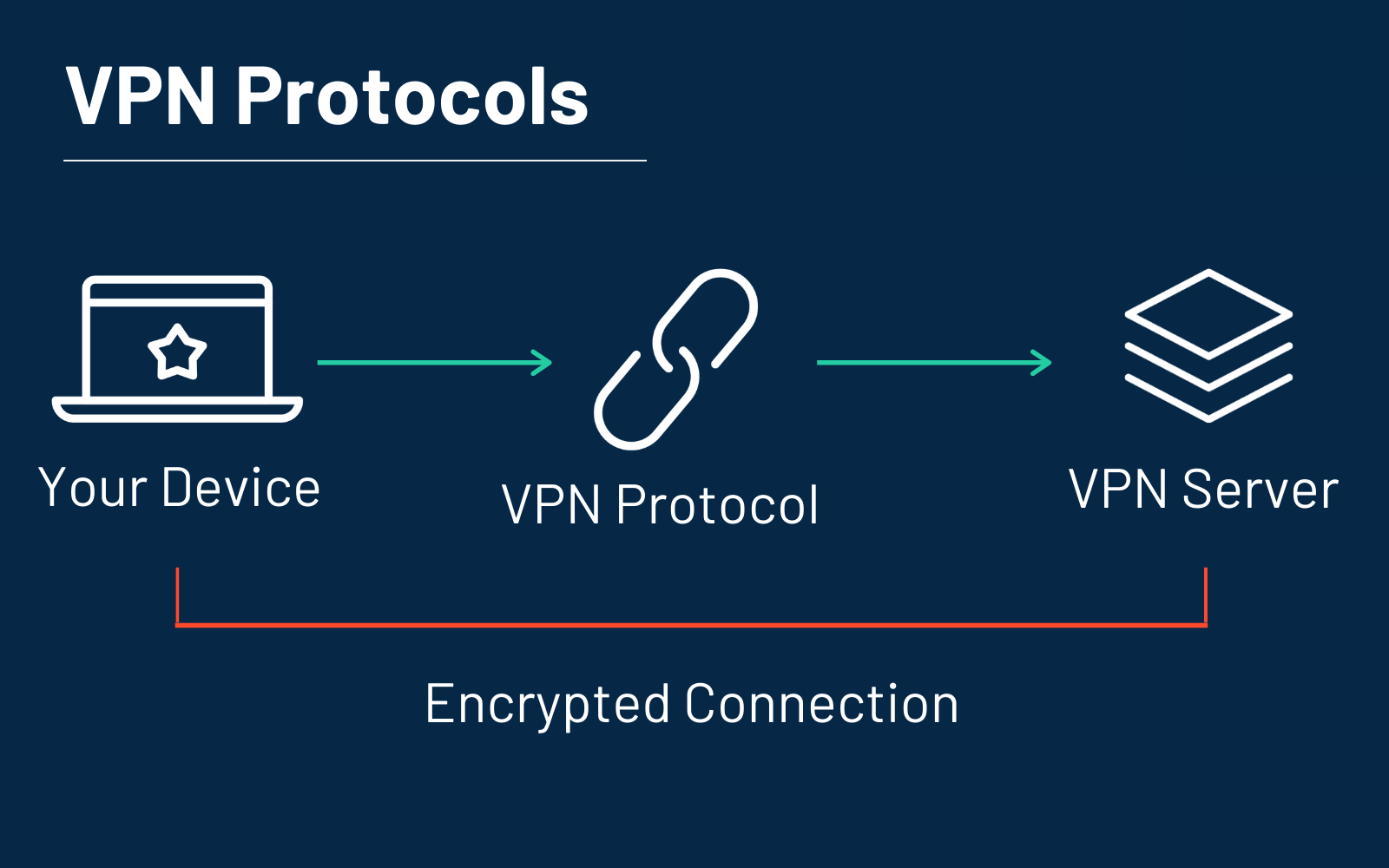
You may already know the full form of VPNs—Virtual Private Networks. But like most things, the VPN has a set of rules and regulations that determine how the VPN is going to work. Basically, VPN has two parts—the VPN client and the VPN server. VPN protocol determines how the data is going to be transferred to your computer by the secret data tunnel that is connected between the VPN client and the VPN server.
The rules that determine the nature of the VPN are known as VPN protocol. Your VPN connection relies on these protocols to deliver a safe and secure connection to your computer. Now, in this post, we are going to learn ‘how many types of VPN protocols are there,’ and ‘how they work.’ By the end of this post, you will have a crystal clear idea about VPN protocols and the different natures of VPNs.
What is the VPN Protocol?
VPNs and VPN protocols are different. If you ask what a VPN is—it is a secured virtual tunnel that allows your computer to connect with an outside server that is unavailable in your location or you want to access with another IP address.
VPN clients can change their IP address and device location to create a connection between your system and the server. But VPN protocols allow the VPN to create connections between a computer and the server. These protocols have different types of rules that work for certain users and their requirements. The VPN protocols also determine the nature of the secret tunnel through their different programs and rules.
Depending on the rules and the nature of the tunnel, VPN providers transmit data through these tunnels and also create a new IP address for your system. Every VPN protocol has different rules and solutions to provide users with a secure internet experience. So, before setting up your VPN service, you need to learn about the VPN protocols and their pros and cons.
What Are the Types of VPN Protocols Out There?
The protocols in the VPN providers deliver different types of security and encryptions. With the secure VPN protocol processes, your device can make a stable connection with the server. However, since not all VPN protocols are the same, it’s important to know which one works in what way. Here, we have shared brief details about each of the VPN protocols in the market so that you know which one to choose.
1. PPTP
The first VPN protocol out there is PPTP or Point-to-Point Tunneling Protocol. The PPTP VPN protocol was developed in the 1990s to support the Windows 95 systems, developed by the famous Microsoft. The main reason for creating this protocol was to allow the users to connect the system to the internet and the intranet.
However, the PPTP protocol is not very powerful and only gets the job done. So, it was also very easy to hack, which causes security risks. Even though the low-encryption feature makes the PPTP protocol fast and effective, it compromises security. That’s why users do not use this protocol much, but you can only choose it to unblock geo-blocked content. However, for other purposes, you should use a more updated VPN protocol.
Pros
- It can be used in various operating systems
- Extremely fast
- Easy to use and set up
- An easy choice for streaming geo-blocked content
Cons
- Security standards are very poor
- Firewalls can easily block this VPN protocol
- Less to no anonymity
- The NSA monitors the PPTP VPN protocol.
2. L2TP/IPSec
The full form of L2TP is Layer Two Tunneling Protocol which is a little better than the PPTP VPN protocol but still outdated. However, the L2TP or IPSec protocol comes with more security features, so it can be considered for your internet browsing purpose. The L2TP/IPSec has two parts in the protocol. The L2TP part is for securing the connection, and the IPSec part encrypts the data. So, the L2TP needs to be connected to the IPSec to provide the full feature of security and privacy to the VPN client.
Since two parts are working together in the L2TP/IPSec VPN protocol, it is naturally slower than the PPTP protocol. Since the internet traffic is going through the standard L2TP form and another encryption layer, it takes much time to connect to your device and deliver the benefits of a VPN. But you can still use the L2TP/IPSec protocol when your primary problem is security and privacy. But if you are looking for something faster, check out the other protocols listed in this post.
Pros
- The L2TP/IPSec is suitable for most modern operating systems
- The VPN protocol protects your data with two types of military standards—L2TP and IPSec
- L2TP protocol does not let the data alter between the sender and receiver while establishing a connection between your system and the server.
Cons
- The L2TP VPN connection is a lot slower than other connections and also uses so much computing power that it jeopardizes your system performance.
- Not easy to set up
- It cannot bypass the firewalls smartly. So, the Surveillance-oriented system administrators can easily track your activities.
3. IPSec/IKEv2
Microsoft and Cisco developed the IKEV2 VPN protocol, which is part of the IPSec internet security. The IKEv2—a short Internet Key Exchange volume 2 uses IPSec to become faster and more secure than the previous two VPN protocols mentioned in this post. The main use of the IPSec/IKEv2 is on mobile devices that run on the 3G or 4G LTE networks.
Hence, with this VPN protocol, your device will get connected to the server no matter what because the IKEV2 is master at establishing secure connections. It can also easily reestablish a drop connection in a matter of seconds. The drop connection usually occurs when the secure tunnel loses its touch with the device. For example, when you are switching from your mobile data connection to WIFI, a connection drop may happen. So, whenever you turn on your hotspot or switch between mobile data to WIFI, the VPN connection will be safe with the IPSec/IKEv2 protocol.
Pros
- The IPSec/IKEv2 VPN connection is fast, stable, and secure
- Can easily handle network changes without a slight drop in performance
- The IPSec and IKEv2 work together to make the VPN connection both fast and reliable
Cons
- Not supported by many devices except for Blackberry
- It does not easily perform on the VPN server-side
4. SSTP
Secure Socket Tunneling Protocol is also developed and managed by Microsoft, which makes it Microsoft Secure Socket Tunneling Protocol (MS-SSTP). However, this VPN protocol is only available for Windows users and was first built for the Windows Vista operating system. The SSTP protocol also works on Linux but has difficulties and challenges that can make your Linux system slower. In this VPN protocol, the traffic goes through a secure socket. The name of the SSTP protocol was extracted from Secure Sockets Layer (SSL) protocol, and the protocol uses the TCP port 443 to bypass firewalls and proxy servers.
So, unlike the PPTP and L2TP protocols, SSTP is not that easy to block by your Windows firewall system. SSTP is secure and supports modern operating systems (Windows, only). But it was actually built for accessing remote connections and does not support general site-to-site VPN access.
Pros
- Remarkably secure and reliable
- Can subdue firewalls easily
- Supports the AES-256 encryption protocol
- Easy to use in Windows since it comes in-built into the Windows Operating Systems
Cons
- Does not support other systems like Mac OS, Android, etc.
- The protocol is not open-sourced; it was not audited
5. OpenVPN
The OpenVPN protocol is one of the majorly used ones by VPN service providers and is effective as well. Unlike the SSTP protocol, it is an open-sourced one and has a GNU Public License that provides the developers access to a source code where they can deal with security flaws. So, the community does not sit back and let the potential security problems ruin the user experience of OpenVPN, but they work on them to improve the protocol.
The OpenVPN protocol uses the OpenSSL that supports 256-bit encryption and comes with two main choices: OpenVPN TCP and OpenVPN UDP. The Transmission Control Protocol or TCP has rules that determine how the connection will go forward while exchanging data through the security panel. And the OpenVPN UDP or User Datagram Protocol transmits the data from the server to the client. There is so much information about how OpenVPN works; to learn about that, you can check out our other articles. But for now, have a look at the pros and cons of OpenVPN. Check out more about OpenVPN and learn how to install it.
Pros
- The OpenVPN protocol is packed with the modern security measures
- Keeps your system and data safe
- The OpenVPN connection appears as normal internet traffic, which makes it easy for it to avoid firewalls
Cons
- Not that easy to configure
- If you configure it incorrectly, the security might be jeopardized.
6. WireGuard
WireGuard is open-sourced like OpenVPN but easier to set up and has a simpler codebase. It has a faster connection advantage, faster speed, more reliability, and modern end-to-end encryption standards. Hence, all these advantages make WireGuard the fastest and newest VPN protocol that beats the advantages of OpenVPN as well as the others.
However, WireGuard is still new and going through incomplete development stages. A few VPN providers such as VPC.ac and TorGuard are currently supporting WireGuard. But NordVPN is testing the WireGuard protocol to see if it does the job of delivering a secure connection to your system or not. And since it is work-in-progress, it might become the next generation of VPN protocols. It is just a matter of time until it does.
Pros
- Faster connection time
- Easy to set up
- Advanced reliability
- Anyone can edit and audit its code since it is an open-sourced protocol
- Can beat OpenVPN in comparison
Cons
- Still incomplete
- Uncertain about what systems it will support
These are the top VPN protocols available at the moment. The first two are outdated and do not complete most of the jobs. And the rest are considered fine. So, check out the other section below to determine which VPN protocol is the best for you.
VPN Protocol Comparison:
If you are looking for a fast VPN protocol to help you unblock geo-blocked websites, go for PPTP. Since PPTP does not have restrictions from so many security measures, it will connect you to the server faster than any other VPN protocol. But if your security matters, you can consider OpenVPN, IPSec/IKEv2, and SSTP. IPSec/IKEv2 are for mobile devices only, so it’s a drawback.
However, SSTP is available for Windows so that you can browse the internet safely on your Windows computer. On the other hand, you are left with OpenVPN since it supports any operating system. OpenVPN runs on Windows, Linux, Mac OS, and so on, and is also fast and reliable.
But before choosing a VPN protocol, you may also consider knowing how many types of VPNs there are. Since the type of VPN determines the type of protocol it uses, it’s worth knowing.
How Many Types of VPNs Are There?
According to the VPN protocol, the VPN client creates a secure and private tunnel connection that connects your device to the internet. Whatever you do from the internet browser after turning on your VPN will only be done through this private tunnel. But two main types of VPNs decide how your connection will work.
Remote Access VPN
With the Remote Access VPN, you can connect to a private virtual network and access its services remotely. Homes and businesses use this type of VPN connection to connect their computer to the internet privately. The Remote Access VPN can help you access geo-blocked content securely and remotely. While you are using these VPNs, no one can know what you are doing on the internet. So, it usually uses OpenVPN, L2TP/IPSec, SSTP, etc., protocols to secure the connection. The Remote Access VPN is not suitable for the PPTP VPN protocol since there is no security measure.
Site-to-Site VPN
These VPNs can extend the company’s network throughout different locations. A Site-to-Site VPN has two parts—intranet-based and extranet-based. The first one combines more than one LAN on a single private network. The second one, or extranet-based, is about extending a company’s network to share it with its customers and partners. Site-to-site VPNs bridge the gap between distant networks and companies through a secure tunnel. These networks can be distant based on their geographical locations. In these VPN services, the VPN client is the router, and the VPN server is also another router. So, it is just Router-to-Router communication.
Conclusion
PPTP is available across multiple platforms, but it is not the safest choice. So, you have left with the rest VPN protocols you can find suitable for your business and home VPN uses.
Among many others, the IKEv2 is the most stable VPN protocol and is up-to-date to reduce runtime crashes. On the other hand, if you eliminate PPTP, SSTP is the easiest-to-use VPN protocol, but it is only available for Windows devices. But if you are looking for a cross-platform VPN protocol, you might want to consider L2TP/IPSec and IKEv2 because these are secure and reliable.
However, choosing a reliable VPN service provider is important. VPN Surf has been acquiring quite a good appreciation from users. You can decide what VPN protocol to use by reading the information we have given in this post. But if you require additional help, please ask us in the comment box below.
Interested in VPN security? Check out this articles now!
- What is a VPN Kill Switch and Why Should You Use It?
- What is SSTP VPN and How Does it Work?
Do you value your privacy online?
Use VPN Surf and surf safely and securely in the open waters of the internet.